Stop the
Secret Sprawl.
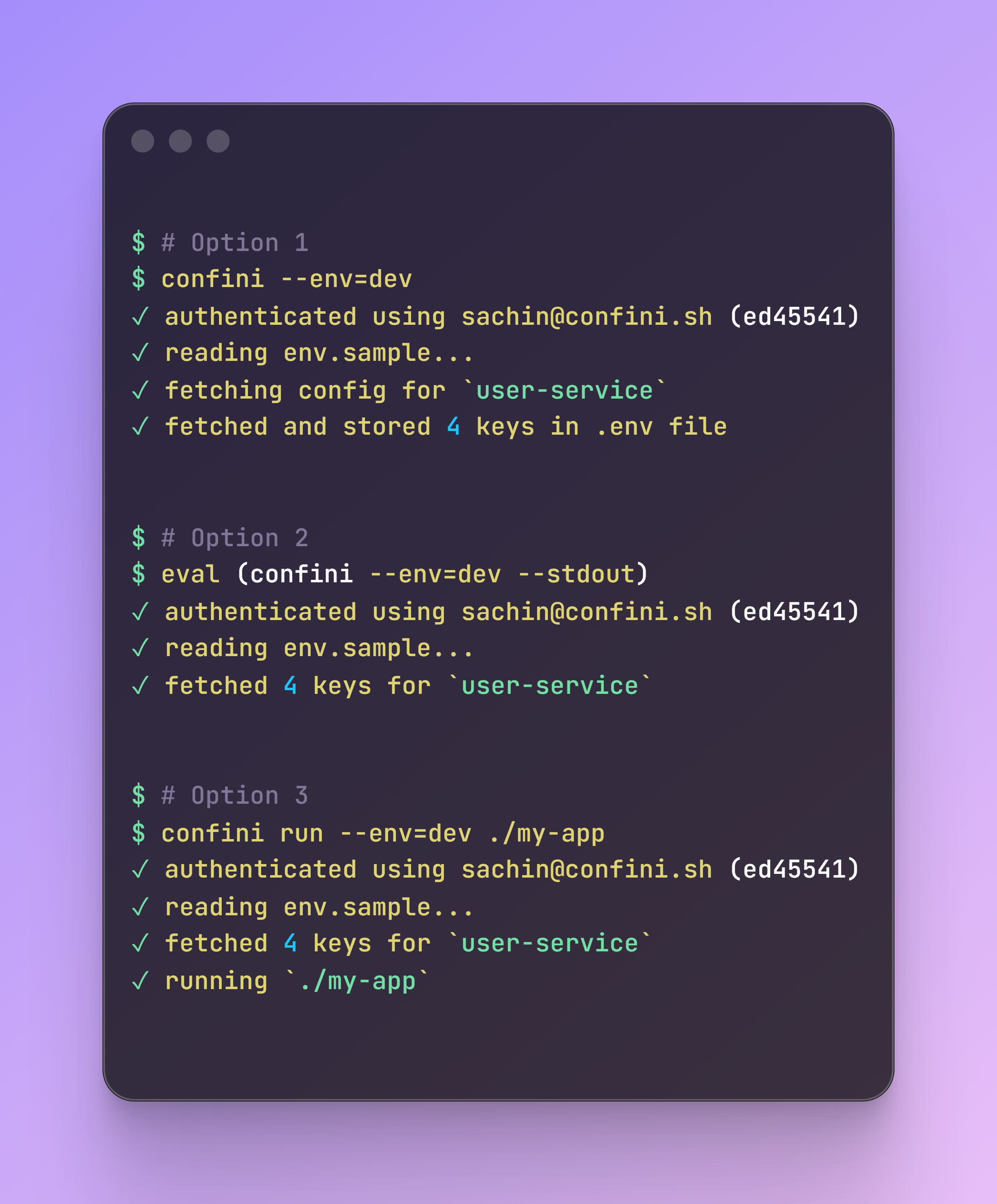
Secure your workflow from Local to Production.
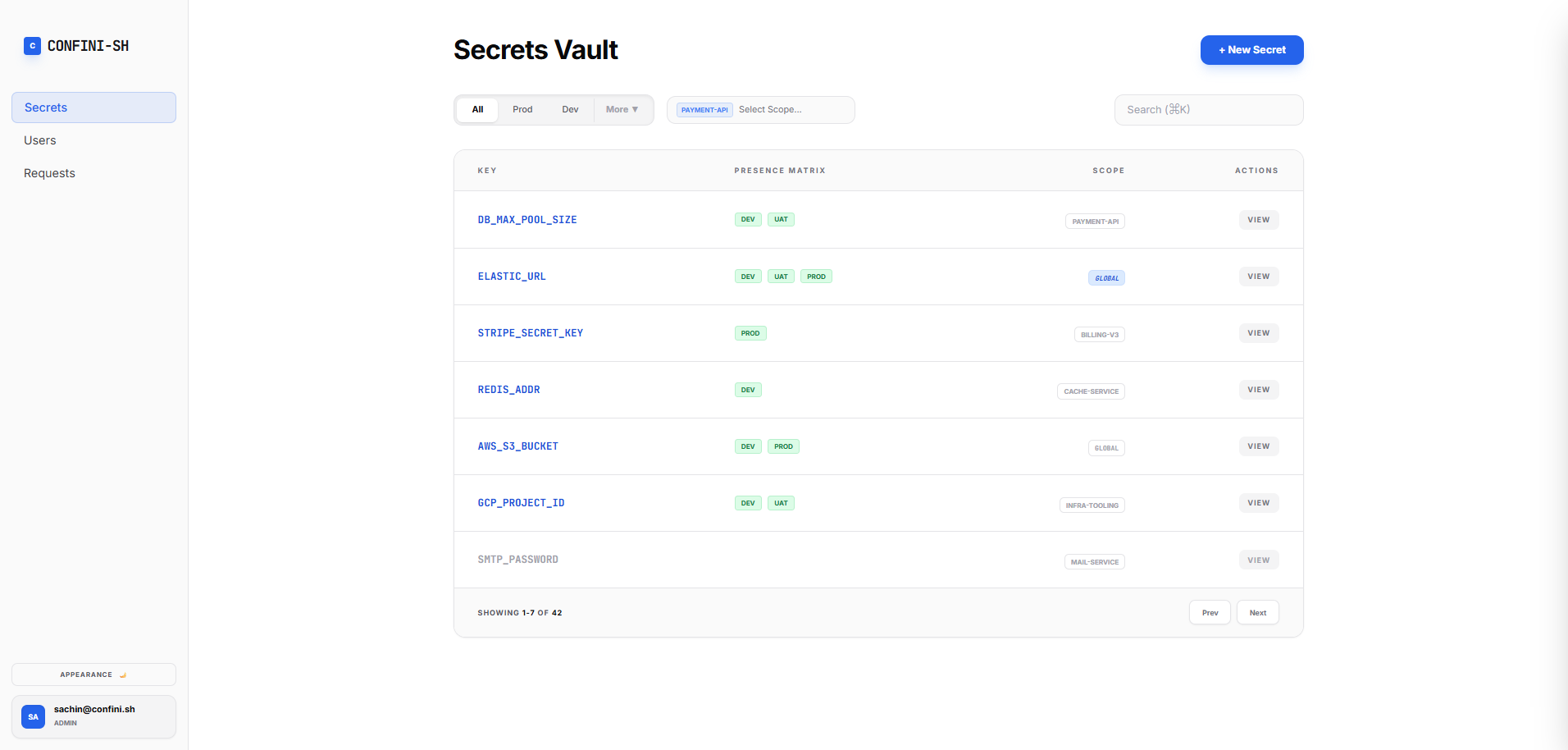
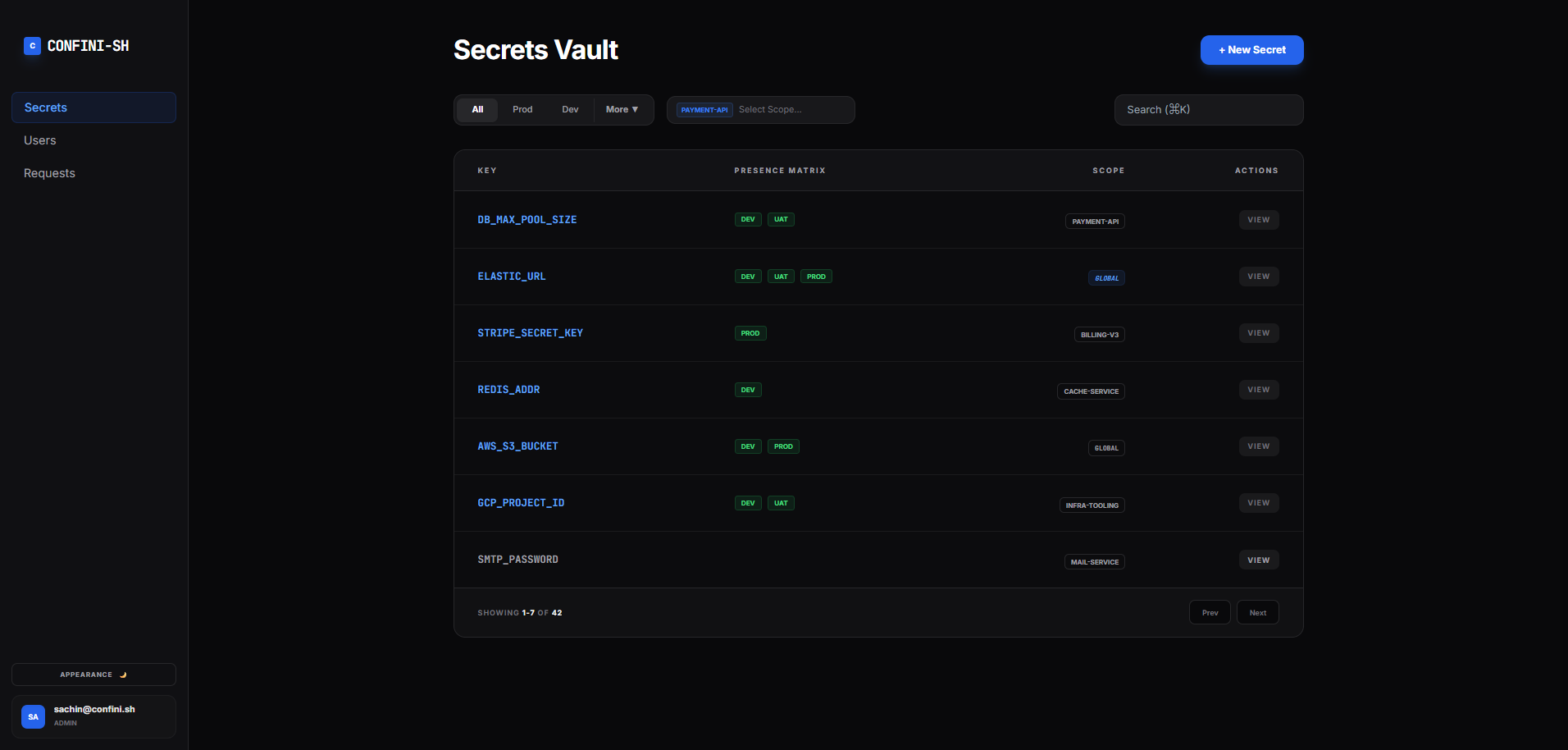
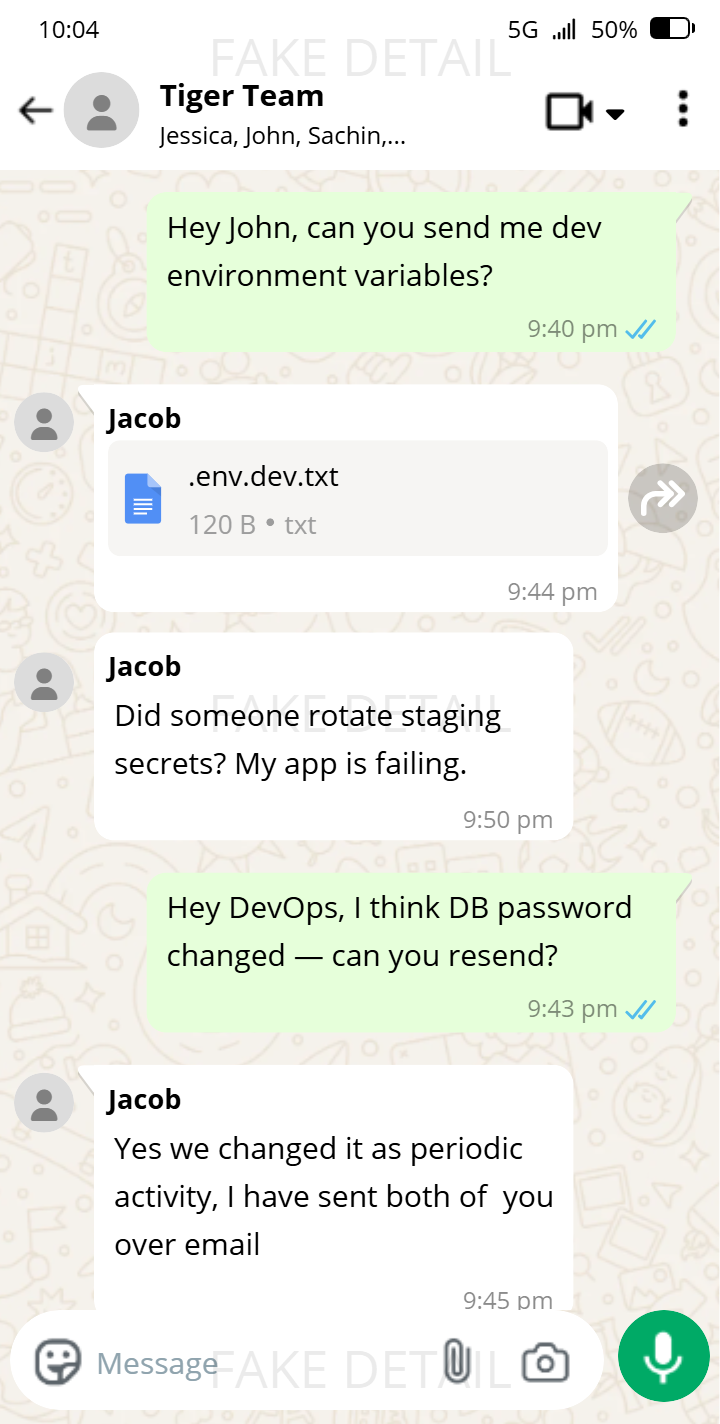
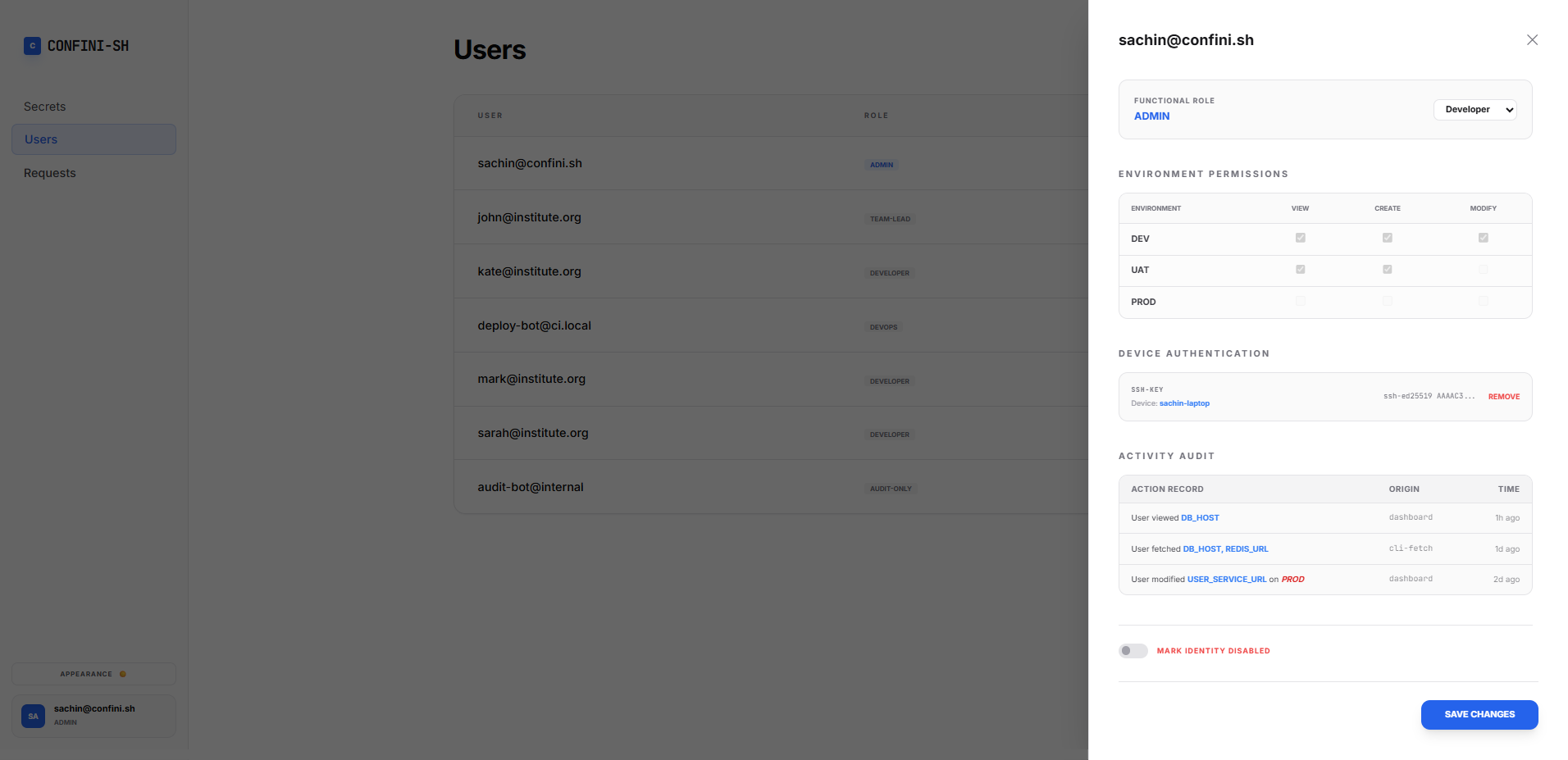
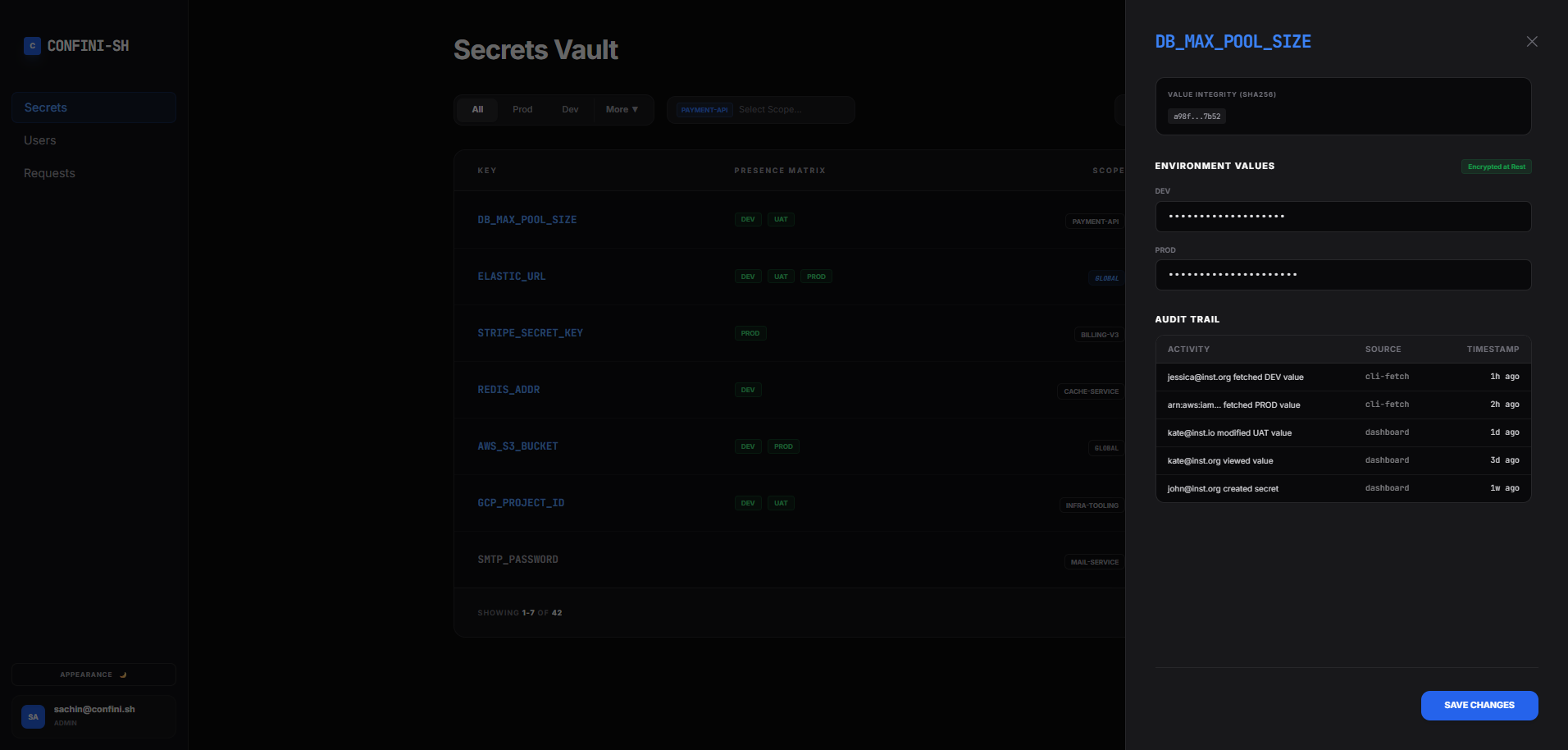
Stop sharing credentials over chat and unmanaged files. confini-sh gives your team a single, secure way to manage secrets across every environment—hosted entirely on your own private infrastructure.
curl -sSf https://confini.sh/install.sh | sh